Building blockchain and trust technologies for mainstream adoption in finance, institutions, and beyond.
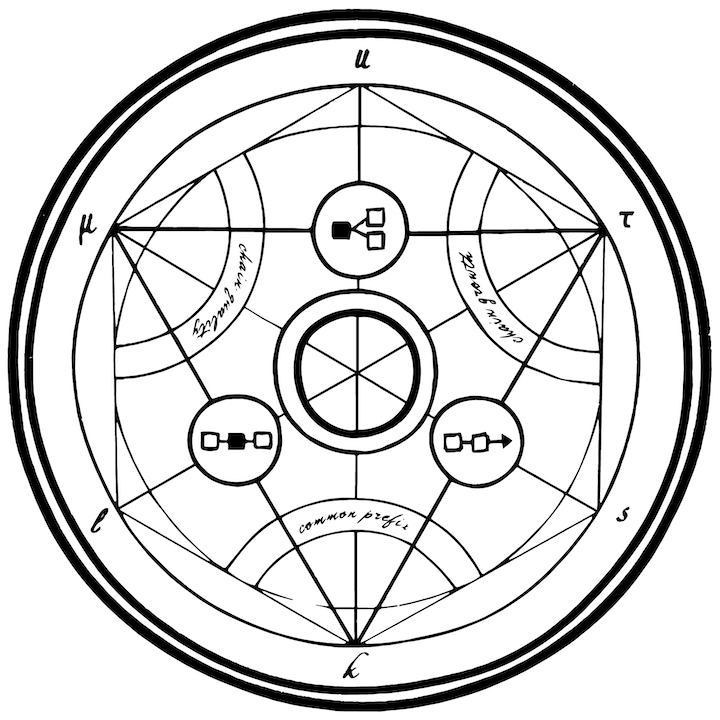
Common Prefix bridges research and engineering to advance the interoperability, usability, and scalability of blockchain and trust technologies. We partner with financial and public institutions, foundations, and blockchain ecosystems to design, audit, and implement secure distributed systems. Our work combines rigorous cryptographic research with practical engineering, designing provably secure systems from first principles and guiding their implementation and deployment.
Team
Our team consists of both academics and industry professionals. On the scientific side, we focus on consensus foundations, with specialists in the areas of proof-of-stake, proof-of-work, auctions, Layer-2s, sharding, channels, bootstrapping, light clients, wallets, smart contracts, interoperability, zero-knowledge, and multiparty computation. On the engineering side, our team comprises experts in smart contract development, testing, and auditing, full-stack software engineering, devops, and operational security. Our team is located across the globe, with members in Athens, Belgrade, Bochum, Copenhagen, Edinburgh, Larnaca, London, Luxembourg, Oslo, Paris, Skopje, Vienna, and Zurich.
Meet the teamPartners
We currently work with companies ranging from Layer-1 blockchains to
dApps and institutions that are reimagining the future of trust technologies. Our services span from theoretical
cryptographic design to hands-on engineering, with our expertise
lying in the junction between both worlds.
At the theory level, we analyze protocol design, define the
desiderata, rigorously document constructions, and pinpoint errors
in the protocols before helping our partners resolve them. In
collaboration with our partner teams, we show that their protocols
are secure from a mathematical point of view, by stating and proving
safety and liveness results in the form of an academic paper.
On the implementation side, we ensure the implementation matches the
theory of the cryptography papers.
Our teams work on auditing, testing, ensuring code quality, and even
on developing smart contracts and other kinds of software for our partners.
At the highest level, we perform due diligence and deliver technical reports,
helping our partners choose the most appropriate and technically sound
partners for their business. Lastly, we aid our partners in securing
their infrastructure by ensuring that their operational security
practices and devops follow the latest industry best practices.
Grants
Common Prefix has received grants from the organizations listed below.